This post may contain affiliate links/ads and I may earn a small commission when you click on the links/ads at no additional cost to you. As an Amazon Affiliate, I earn from qualifying purchases. Techsphinx also participates in the StationX Affiliate program. You can read my full disclaimer here.
Cybersecurity consists of various types of pen testing, like website, mobile app, wireless etc. This article will focus on the best wireless hacking hardware that you can use for wireless penetration testing.
For categories like website and application pen testing, you need software tools to find vulnerabilities and exploit them. However, in the case of Wireless, you will need hardware tools to capture wireless packets or interact with radio frequencies.
In my other article, I mentioned various WiFi hacking hardware tools. This post will cover hacking devices that can also interact with other wireless protocols like Bluetooth, NFC, GPS, ZigBee and RFID.
Disclaimer
Here are a few points, I would like you to consider before proceeding with this post.
1. These Wireless hacking hardware devices are made for ethical purposes, do not use them for harming someone. I/TechSphinx shall not be held responsible for your actions.
2. You can buy these devices from their official websites or Amazon. I have provided (Affiliate) links to Amazon for every device mentioned in this post.
3. Make sure, the use of these devices is not banned in your country.
Now, let’s have a look at the best Wireless hacking hardware devices.
Best Wireless Hacking Hardware Tools
1. HackRF One

HackRF One is an open-source hardware platform from Great Scott Gadgets. This software-defined radio is designed to test, develop and modify contemporary RF (Radio Frequency) systems.
The unit is capable of transmitting and receiving radio signals from 1 MHz to 6 GHz. It works as a USB peripheral and can be even programmed as a stand-alone device.
The HackRF One can interact with a broad range of wireless systems which include:
- Broadcasting Stations
- Wi-Fi
- Bluetooth
- Smartphones
- GPS
If you plan to pentest Radio Frequencies, then this is a must-have tool in your wireless hacking hardware toolkit.
2. Flipper Zero
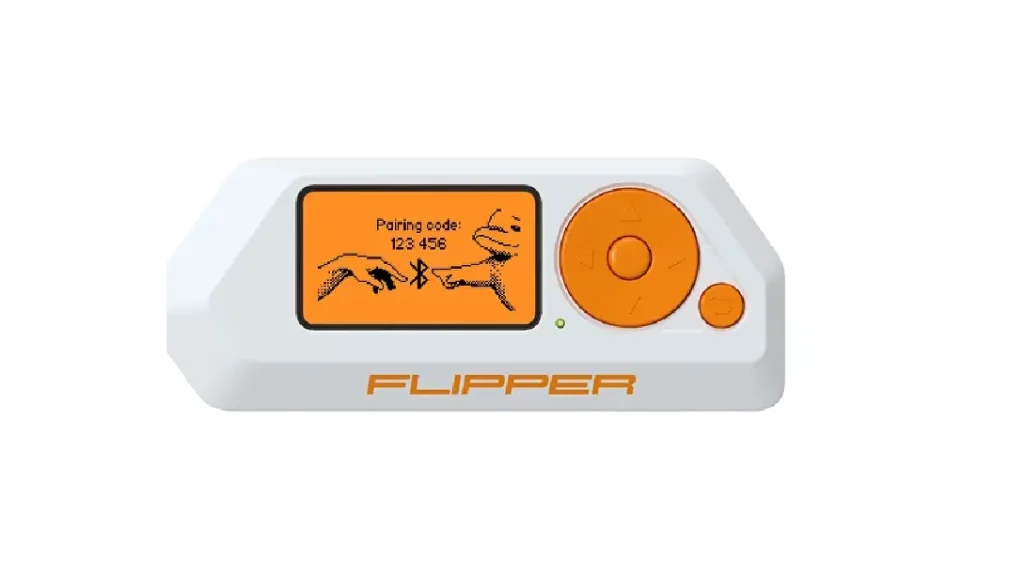
Flipper Zero is a fully open-source and portable tool for pen-testers. You can use this device to pentest radio protocols, RFID, 1-Wire protocol, access control systems and even debug the hardware using the GPIO pins.
Everything is packed into a portable toy-like box and you can access all its functionality using the 5-button directional pad and the 1.4″ monochrome LCD.
Although Flipper Zero is a completely independent gadget that doesn’t require any additional devices, you can still extend its functionality by connecting it to other devices via the USB port or the GPIO Pins. It also ships with a 2000 mAh battery that can last up to 7 days (depending on usage).
If you are in the market for a Swiss-army knife (in terms of hacking), then Flipper Zero will be the best choice.
3. Ubertooth One

The Ubertooth One is an open-source Bluetooth pentest tool from Michael Ossmann. It is bundled with an ARM Cortex M3 microcontroller and an antenna.
It has an operating frequency of 2.4 GHz. You can plug this tool into a computer using the USB and use it with various wireless monitoring tools like Kismet.
Compared to other Bluetooth monitoring tools that may cost you more than $1000, this tool is very cheap. The best part of Ubertooth One is both the software and hardware of this device are open-source, therefore you can even build one yourself.
4. HiLetgo Zigbee CC2531 Sniffer

Zigbee is a cheap and low-power wireless network standard used to create personal area networks with small, low-power digital radios, such as for home automation, medical device data collection, and other low-power low-bandwidth needs.
It is an IEEE 802.15.4-based specification and due to its low power consumption, the range is limited to 10-100 Meters. However, Zigbee devices can transmit data over long distances by passing data through a mesh network of intermediate devices to reach more distant ones.
The Zigbee sniffer is designed to sniff on devices that use a Zigbee Chipset.
So, if you are interested in hacking security systems, home automation tools, drones, wireless sensors etc. then this wireless hacking hardware will help you to sniff and decode the packets.
5. Crazyradio PA

Devices like a wireless keyboard and mouse send mouse movements and keystrokes over the air. An attacker can compromise a victim’s computer by transmitting specially crafted radio signals using a device like CrazyRadio PA.
Crazyradio PA is an open USB radio dongle based on nRF24LU1+ technology from Nordic Semiconductor. This device allows an attacker to exploit vulnerabilities like “Mousejack” and “Keyjack” from a distance of 1km and one can even extend the range using a Wi-Fi booster antenna.
Wireless hacking hardware that allows taking control of the target computer is a must-have in any hacker’s pen-testing toolkit.
6. Proxmark3

The Proxmark3 is developed for sniffing, reading and cloning RFID (Radio Frequency Identification) tags. It is the best device available on the market when it comes to RFID pen-testing.
The Proxmark 3 RDV4 is the latest revision of the Proxmark 3 Platform as of writing this post. The device is small enough to fit in a pocket and is also compatible with Android.
Since RFID is used in a variety of applications including commerce and transportation, it has become a target for many potential attacks.
If you are learning about physical security, then I recommend this wireless hacking hardware be included in your pen-testing toolkit.
7. Wi-Fi Pineapple

WiFi Pineapple is a powerful and versatile wireless auditing platform from hak5. It contains many sets of tools for wireless penetration testing which is very helpful for network security administrators.
WiFi Pineapple can also be used as a “Rouge Access Point”, thereby enabling targeted “Man-In-The-Middle” attacks. You can also conduct active WiFi attacks with manipulated management frames including deauth.
Not only that, but WiFi Pineapple is also a great tool for advanced reconnaissance like identifying vulnerable devices, Monitoring and collecting data, gathering intelligence on targets etc.
The best part of this tool is that you don’t have to install any software to use it. Everything can be done through an intuitive web interface with just a few clicks.
There is also a very active community surrounding it with constant updates making it the most well-known and classic tool when it comes to pen-testing Wi-Fi networks.
8. Wi-Fi Deauther

De-authentication is necessary for hacking Wi-Fi networks. Once you de-authenticate a client from a wireless network, the client is forced to re-authenticate with the network.
During re-authentication, an attacker can steal the WPA handshake and use it to brute-force the password for the network.
Also, de-authentication is useful in “Evil Twin” attacks, where the attacker disconnects the client from the wireless network and forces the client to authenticate to a “Rouge Access Point”.
DSTIKE WiFi Deauther Board is a small and cheap de-authentication tool that is bundled with ESP8266 Deauther software. With this tiny development board, you can perform different attacks to test WiFi networks.
This device is also available as a smartwatch with an OLED Display and has the same ESP8266 chip. The latest version (v3) of the WiFi Deauther Wristband has an 800mAh lithium battery that gives up to 8-10 hours of working time.
Note: The ESP8266 only supports 2.4GHz frequency.
9. DSTIKE WIFI Duck

You’ve probably heard of or seen USB rubber ducky (especially if you are a Mr Robot fan).
USB rubber ducky is a tool that looks like a flash drive but acts as a keyboard and allows an attacker to execute keystroke injection attacks on target computers.
Now, in the case of a USB rubber ducky, an attacker has to program the payload in advance. If the attacker doesn’t know which commands to run beforehand, then USB rubber ducky is useless.
This is where DSTIKE WIFI Duck comes into play. WiFi Duck does the same thing as USB Rubber Ducky but has Wi-Fi access and a web interface. This means you can control it remotely over WiFi from a distance.
Now, an attacker can easily send payloads and commands over the WiFi to the target machine as long as the WiFi Duck is connected. An attacker can also use this device to inject backdoors into the target machine, so even if WiFi Duck is disconnected the target machine will still be under the control of the attacker.
Note: Unlike Crazyradio PA, you have to physically attach this device to the target computer and control it via a web interface on the attacker’s machine.
10. Alfa AWUS036ACH USB Wi-Fi Adapter

A wireless adapter is the most useful tool to connect to a Wi-Fi network. Laptops have inbuilt Wi-Fi adapters.
However, not all Wi-Fi adapters are suitable for hacking. They do not support packet injection or monitor mode which is essential for tools like “aircrack-ng” to work properly.
In this situation, you’ll need to rely on an external/USB wifi adapter.
Alfa AWUS036ACH USB Wi-Fi Adapter is bundled with Realtek RTL8812AU chipset which is compatible with both 2.4 and 5 GHz wavelength.
Please note that the Alfa AWUS036ACH is not a plug-and-play adapter. You may need to manually install the Realtek drivers. In some operating systems, like Kali Linux, it’s pretty straightforward and you’ll also find plenty of tutorials for the same on Youtube.
If you are planning to use this adapter on any other Linux system than Kali Linux, I recommend you check if the adapters have drivers available for your particular OS before purchasing.
I have also made a dedicated list of USB WiFi adapters for Kali Linux. Have a look at this list, if you want alternatives.
11. Raspberry Pi

The Raspberry Pi is a low-cost, credit-card-sized computer that plugs into a computer monitor or TV and uses a standard keyboard and mouse.
Now, Raspberry Pi is not particularly made for hacking purposes but you can install Kali Linux on it and turn it into a portable Wi-Fi hacking device.
Kali Linux has many different software tools to not only hack Wi-Fi but for hacking anything in general. That’s why most hackers prefer Kali Linux as their prime OS for pen testing.
Although you can install Kali Linux on your Laptop, it is not a good idea to use a device that you use for your day-to-day work and contains your personal data.
So, either you carry a different laptop or go for a much cheaper option – a Raspberry Pi.
I have also written a complete guide on installing Kali Linux on Raspberry Pi.
Conclusion
I hope this list helps you to find the right wireless hacking hardware for your pen-testing needs.
Using some of these tools might not be easy and there may be a learning curve. However, these are some of the most popular Wireless Hacking hardware one should have in their pen testing arsenal.
If you like this post, then follow Techsphinx on Facebook and Twitter for more reviews, tricks, tips and tutorials.
This article needs update or correction? Report the issue here so I can update it.





