This post may contain affiliate links/ads and I may earn a small commission when you click on the links/ads at no additional cost to you. As an Amazon Affiliate, I earn from qualifying purchases. Techsphinx also participates in the StationX Affiliate program. You can read my full disclaimer here.
Let me start by asking you a simple question. Imagine, you and your friend are connected to a WiFi network and you want to disconnect your friend from using the said WiFi network. How will you achieve that without having physical access to your friend’s device or having any administrator access to the router/access point?
The answer is – through a de-authentication attack. A Wifi de-authentication attack target communication between a Wireless access point and devices that are connected to that access point.
In a de-authentication attack, an attacker sends de-authentication frames to the target/s with a spoofed MAC address of the access point. Thereby, disconnecting the target/s from that access point.
A WiFi deauther is a device that can perform the said de-authentication attack.
Now, you can also perform a de-authentication attack using a compatible WiFi adapter (one that supports monitor mode and packet injection). However, you also need an operating system running on Laptop/PC/Raspberry Pi to use the WiFi adapter for a de-authentication attack.
Using an ESP8266 board that is programmed for de-authentication attacks will be a much more suitable and standalone option. Especially, if you want to only perform a de-authentication attack.
Update (Jan 2023): Added DSTIKE Deauther Hackheld.
Here’s the summary of the best WiFi deauther:
| WiFi Deauther | Link to Product |
|---|---|
| AURSINC WiFi Deauther & Bad USB Watch V4 | See details at Amazon |
| DSTIKE Monster V5 WiFi Deauther | See details at Amazon |
| DSTIKE Deauther Hackheld | See details at Amazon |
| DSTIKE Mini WiFi Deauther | See details at Amazon |
What is the benefit of a WiFi Deauthentication Attack?
Other than disconnecting clients from a WiFi network, de-authentication is necessary for hacking Wi-Fi networks. Once you de-authenticate a client from a wireless network, the client is forced to re-authenticate with the network.
During re-authentication, an attacker can steal the WPA handshake and use it to brute-force the password for the network.
Also, de-authentication is useful in “Evil Twin” attacks, where the attacker disconnects the client from the wireless network and forces the client to authenticate to a “Rouge Access Point”.
If you want to learn about WiFi hacking, then I recommend you check out The Complete Ethical Hacking Course Bundle on StationX.
Even better! You can sign up for the StationX VIP membership and gain access to the full library of top courses (230+ courses) related to cyber-security along with many other great benefits. You can read more about the membership and its advantages here.
Disclaimer
1. WiFi deauthers are made for ethical purposes, do not use them for harming someone. I/TechSphinx shall not be held responsible for your actions.
2. You can buy these deauthers from their official websites or Amazon. I have provided (Affiliate) links to Amazon for every device mentioned in this post.
3. All products mentioned here use the ESP8266 module. ESP8266 only supports the 2.4 GHz frequency.
4. Make sure, the use of WiFi deauther is not banned in your country/locality.
Best WiFi Deauther
1. AURSINC WiFi Deauther & Bad USB Watch V4

The first on the list is the AURSINC WiFi Deauther (v4) D&B watch. Unlike previous versions of this watch (v3 and below), this watch includes both ESP8266 and Atmega Atmega32u4. Therefore, it can perform both de-authentication and bad USB attacks.
A BadUSB attack uses the USB interface to discreetly execute commands or run malicious programs on the victim’s computer. The two buttons included (Digital Pin 9 and 10) on the watch can be used to execute different commands. All this can be programmed using the Arduino IDE.
As for the deauther part, it is equipped with an external 3dB antenna for better signal strength. Moreover, you can replace the default antenna with a larger antenna on the SMA connector for increased signal strength.
A 1000 mAH battery is included that can last up to 10 hrs (depending on your usage). Other than that, there are empty solder pads at the back of this watch which can be soldered to connect ESP8266 with atmega32u4.
You can solder the ICC pads and turn this device into a WiFi duck.
If you want a WiFi deauther watch, then this D&B watch will be the best choice. Not only it’s a cool WiFi hacking device, but it is also very handy as compared to the WiFi Deauther boards mentioned below.
2. DSTIKE Monster V5 WiFi Deauther

The second on the WiFi deauther list is the DSTIKE Monster V5. It is installed with the latest ESP8266 Deauther software through which you can perform different attacks to test WiFi networks.
It uses an 8db antenna for wireless connectivity. Apart from the antenna, it also ships with 10P Pinheader, Screw, 4×4 Support, Arcylic case, Battery connector and Battery wire.
Disconnecting WiFi (2.4GHz), creating fake networks, confusing wifi trackers, displaying wifi traffic and showing time are the functions this Dstike Monster V5 can perform.
It also comes with an integrated 18650 charging system. Therefore, you can use two 18650 batteries with the Monster V5. Moreover, it contains a USB Output, 4 Flashlight LED, OLED display and a 3-way momentary slide switch.
DSTIKE Monster V5 is an upgrade to the DSTIKE Deauther OLED V6 that ships with a 1 x 18650 battery system, 1 LED and no USB output.
Although, it is not cool as the WiFi Deauther Watch mentioned previously, but at this price, Monster V5 is a great deauther board that you can use to have fun with your WiFi network.
3. DSTIKE Deauther Hackheld

If you didn’t fancy the deauther watch, then maybe this hand.. I mean hackheld deauther might be of interest to you.
The DSTIKE deauther hackheld (aka Hackheld vega) is a simple handheld WiFi deauther tool made using a D1 mini board, OLED, RGB LED and a couple of buttons. All the parts are packed in an acrylic case.
It ships with the latest ESP8266 Deauther software that can be used to perform different functions such as disconnecting the WiFi, creating fake networks, confusing wifi trackers and monitoring wifi traffic.
Just as the previously mentioned Deauther watch, the deauther hackheld is also equipped with a 1000 mAH battery that can last up to 10 hrs (depending on your usage).
Although not as jam-packed as the deauther watch, for this price, Hackheld Vega is a great WiFi deauther tool that you can use to pentest your WiFi networks.
Moreover, if you are a DIY enthusiast, then you can also build your own Hackheld Vega. You can find more info on SpacehuhnTech’s Hackheld GitHub repo.
4. DSTIKE Mini WiFi Deauther
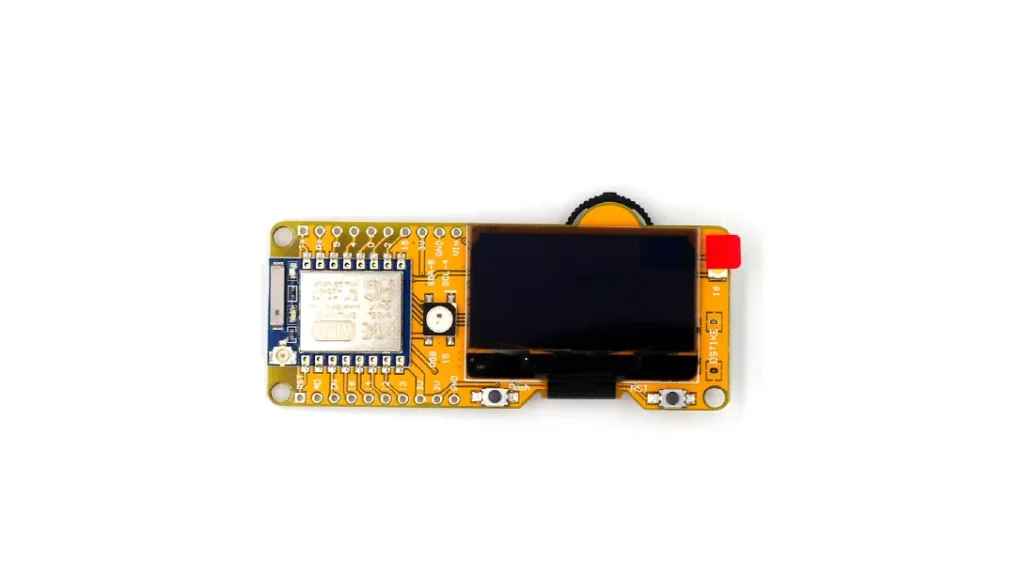
The last on the best WiFi deauther list is the DSTIKE Mini deauther board. Just like the previously mentioned Monster V5, this one also ships with the latest ESP8266 Deauther software.
It includes a 5dB antenna for wireless connectivity, a battery connector and a female header.
Moreover, DSTIKE Mini has power saving and safety features such as a low voltage low-dropout regulator, short protection, over-charging protection and over-temperature protection.
Not as feature-packed as the WiFi deauther mentioned previously, however, if you’re on a tight budget, then DSTIKE Mini would be the optimum WiFi Deauther board for your pentesting needs.
FAQs about WiFi Deauther
A WiFi Deauther is a device or software tool designed to send de-authentication packets to wireless networks, disrupting the connection between devices and the network. It’s often used for testing and security research purposes.
WiFi Deauthers are used by security professionals, researchers, and enthusiasts to analyse vulnerabilities in wireless networks. They help identify weak points in network security, test the resilience of devices, and assess the effectiveness of security measures.
While WiFi Deauthers can be valuable for ethical hacking and security research, their use might be subject to local laws and regulations. Using them without the proper authorization on networks you don’t own or have permission to test could potentially violate laws.
A WiFi Deauther sends de-authentication frames to targeted devices on a network, making them temporarily lose connectivity. This is achieved by impersonating the access point and sending packets that request the target devices to disconnect and then reconnect to the network.
No, WiFi Deauthers can be used for both malicious and legitimate purposes. While some attackers might use them for unauthorized access or denial-of-service attacks, ethical hackers and researchers use them to expose vulnerabilities and improve network security.
WiFi Deauthers themselves are not designed to steal data directly. However, they can be a part of a larger attack strategy to create a window of opportunity for other attacks (such as man-in-the-middle attacks) if the network’s security is weak.
Conclusion
This concludes the best WiFi deauther list. I have also written other posts on WiFi hacking hardware, that contains many other great devices for WiFi pentesting.
If you are interested in wireless hacking (including WiFi, Bluetooth, RFID etc.) devices, then you can check my Wireless Hacking Hardware devices list for the same.
If you like this post, then follow Techsphinx on Facebook and Twitter for more reviews, tricks, tips and tutorials.
This article needs update or correction? Report the issue here so I can update it.





